"Safeguard your digital assets with our comprehensive cybersecurity solutions, delivering robust protection against evolving threats."
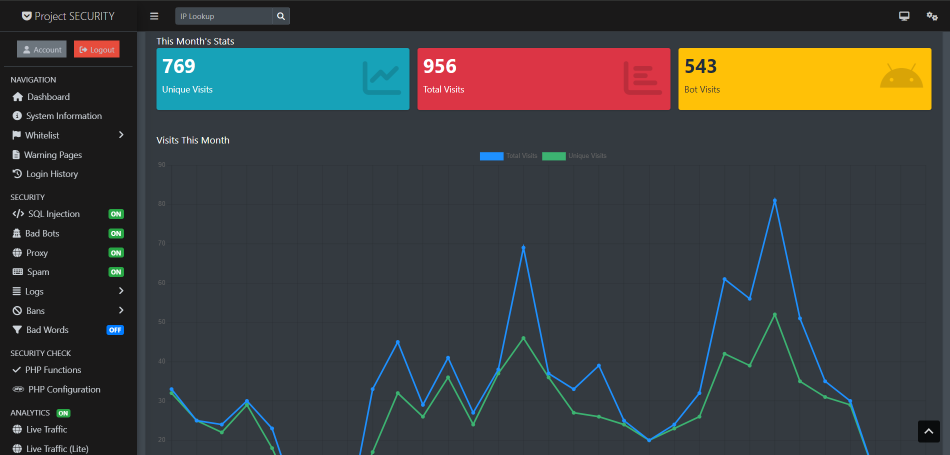
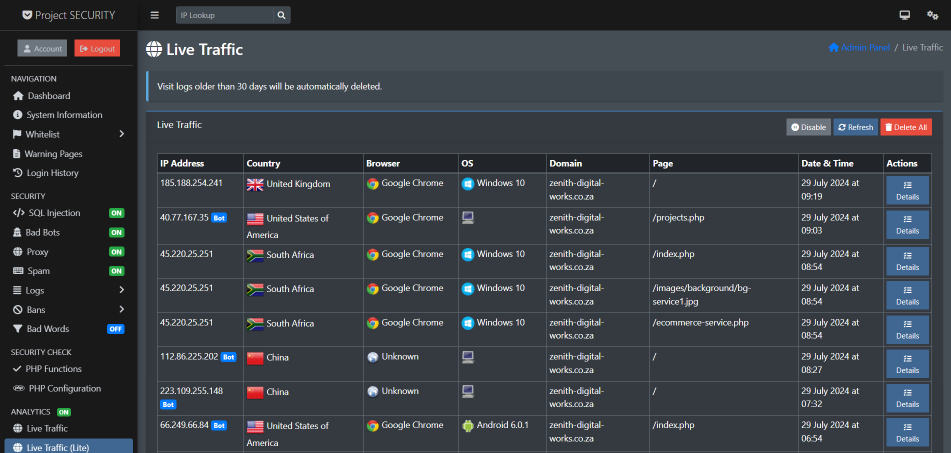
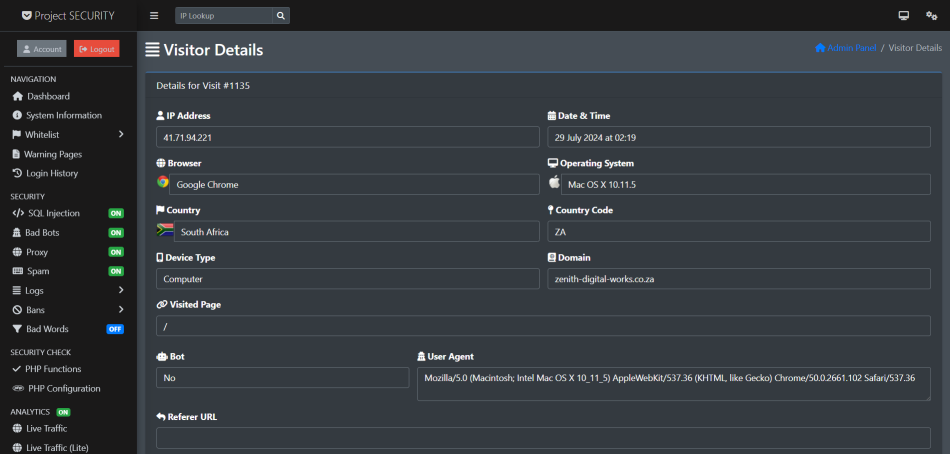
* Threat monitoring and detection - Continuous monitoring of networks, systems, and applications to identify and respond to potential threats in real-time.
* Vulnerability management - Identifying, assessing, and remediating security vulnerabilities across the IT infrastructure.
* Incident response and remediation - Processes and capabilities to quickly contain, investigate, and recover from cybersecurity incidents.
* Security architecture and engineering - Designing, implementing, and maintaining secure systems, networks, and applications.
* Security awareness and training - Educating employees on cybersecurity best practices to reduce the human risk factor.
* Compliance and governance - Ensuring adherence to relevant security standards, regulations, and industry frameworks.